Are Humans to Blame? Science Is Out

Marcus Yam for The New York Times
The water rose at Battery
Park. Scientists said they did not know for sure if Hurricane Sandy
could be tied directly to climate change, a question on the minds of
many along the storm’s path. More Photos »
By JUSTIN GILLIS
Published: October 31, 2012
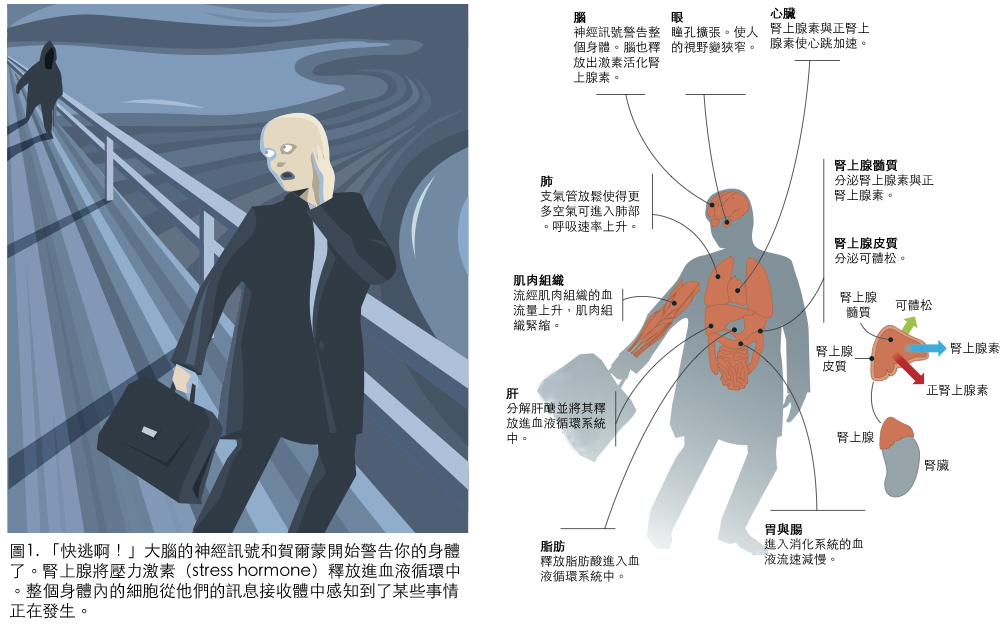
From the darkened living rooms of Lower Manhattan to the wave-battered
shores of Lake Michigan, the question is occurring to millions of people
at once: Did the enormous scale and damage from Hurricane Sandy have anything to do with climate change?
Multimedia
Related
-
New York Region Faces Rescues, Looting and a Rising Death Toll (November 1, 2012)
-
New Jersey Is Reeling From Punch by a Storm (November 1, 2012)
Lindsay Niegelberg/The Stamford Advocate
A hurricane barrier in Stamford, Conn. Experts say
that the storm, whatever its causes, should be seen as a warning.
More Photos »
Hesitantly, climate scientists offered an answer this week that is
likely to satisfy no one, themselves included. They simply do not know
for sure if the storm was caused or made worse by human-induced global
warming.
They do know, however, that the resulting storm surge along the Atlantic
coast was almost certainly intensified by decades of sea-level rise
linked to human emissions of greenhouse gases. And they emphasized that
Hurricane Sandy, whatever its causes, should be seen as a foretaste of
trouble to come as the seas rise faster, the risks of climate change
accumulate and the political system fails to respond.
“We’re changing the environment — it’s very clear,” said Thomas R. Knutson, a research meteorologist with the government’s Geophysical Fluid Dynamics Laboratory
in Princeton, N.J. “We’re changing global temperature, we’re changing
atmospheric moisture, we’re changing a lot of things. Humans are running
this experiment, and we’re not quite sure how it’s going to turn out.”
By the time Hurricane Sandy hit the Northeast coast on Monday, upending
lives across the Eastern half of the country, it had become a freakish
hybrid of a large, late-season hurricane and a winter storm more typical
of the middle latitudes. Though by no means unprecedented, that type of
hybrid storm is rare enough that scientists have not studied whether it
is likely to become more common in a warming climate.
“My profession hasn’t done its homework,” said Kerry A. Emanuel,
a climate scientist at the Massachusetts Institute of Technology. “I
think there’s going to be a ton of papers that come out of this, but
it’s going to take a couple of years.”
Scientists note that a warmer atmosphere can hold more water vapor,
which in principle supplies more energy for storms of all types. The
statistics seem to show that certain types of weather extremes, notably
heat waves and heavy downpours, are becoming more common.
But how those general principles will influence hurricanes has long been
a murky and contentious area of climate science. Most scientists expect
that the number of Atlantic hurricanes will actually stay steady or
decline in coming decades as the climate warms, but that the proportion
of intense, damaging storms is likely to rise.
The experts differ sharply on whether such a rise can already be
detected in hurricane statistics. Recent decades seem to show an
increase in hurricane strength, but hurricanes tend to rise and fall in a
recurring cycle over time, so it is possible that natural variability
accounts for the recent trends.
Jeff Masters, a meteorologist and founder of a popular Web site, Weather Underground,
suspects some kind of shift is under way. The number of hurricanes and
tropical storms over the past three years has been higher than average,
with 19 named storms in both 2010 and 2011 and 19 so far this hurricane
season, which ends Nov. 30. According to the National Hurricane Center
there are, on average, 12 named storms each season.
“The climatology seems to have changed,” Dr. Masters said. “We’re
getting these very strange, very large storms with very low central
pressures that don’t have that much wind at the surface.”
Hurricanes draw their energy from warm waters in the top layer of the
ocean. And several scientists pointed out this week that parts of the
western Atlantic were remarkably warm for late October as Hurricane
Sandy passed over, as much as 5 degrees Fahrenheit warmer than normal
for this time of year.
Kevin E. Trenberth, a scientist with the National Center for Atmospheric Research
in Boulder, Colo., said that natural variability probably accounted for
most of that temperature extreme. But, he added, human-induced global
warming has raised the overall temperature of the ocean surface by about
one degree Fahrenheit since the 1970s. So global warming probably
contributed a notable fraction of the energy on which the storm thrived —
maybe as much as 10 percent, he said.
Dr. Trenberth said that many of Sandy’s odd features, including its
large scale, derived from its origin as a merger of two weather systems
that converged in the western Atlantic.
“My view is that a lot of this is chance,” he said. “A hybrid storm is
certainly one which is always in the cards, and it’s one we’ve always
worried about.”
Winds knocked out power as far west as Michigan. But the most serious
damage, including the flooding of New York’s subway tunnels and the
broad destruction along the Jersey Shore, came as the storm pushed
roiling ocean waters onto land, a phenomenon known as storm surge. The
surge set records in some places, including the Battery in Lower
Manhattan.
Globally, the ocean rose about eight inches in the last century, and the
rate seems to have accelerated to about a foot a century.
Scientists say most of the rise is a direct consequence of human-induced
climate change. Ocean water expands when it warms, accounting for some
of the rise, and land ice is melting worldwide, dumping extra water into
the ocean. Scientists say they believe the rate will accelerate
further, so that the total increase by the end of this century could
exceed three feet.